Drop a file to seal it
Select any file to create a cryptographic seal. The file is streamed through BLAKE3 in your browser, building a Merkle tree from 64KB chunks. Only the cryptographic manifest is sent to the server.
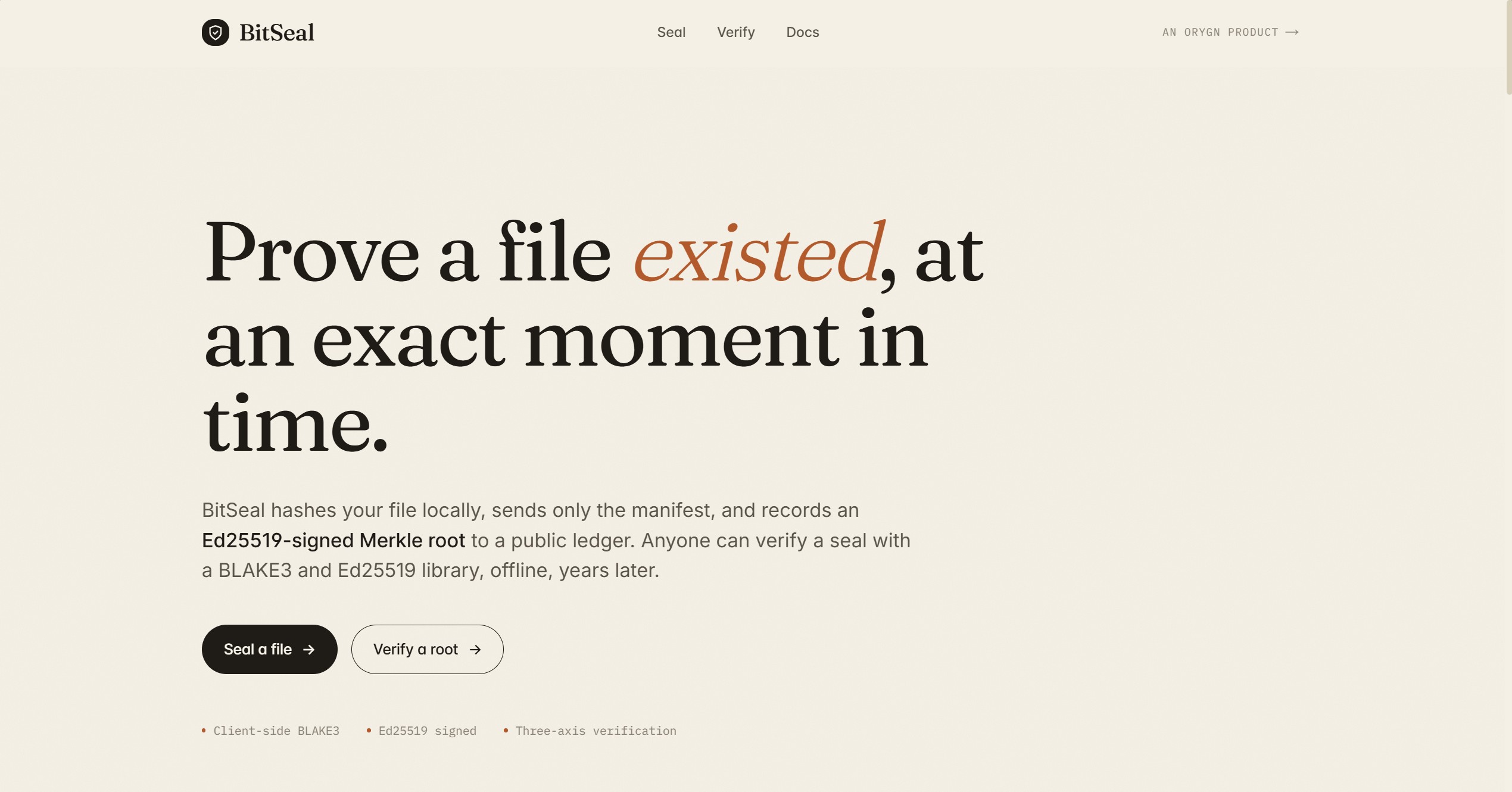
BitSeal hashes files in the browser with BLAKE3, signs the Merkle root with an Ed25519 Authority key, and anchors the seal to the Bitcoin blockchain via OpenTimestamps. The file bytes never leave your device. Seals persist in a Neon Postgres ledger and can be verified offline with standard cryptographic libraries.
How it works
BitSeal streams your file through BLAKE3 in the browser, builds a Merkle tree from 64KB leaves, and sends only the cryptographic manifest to the server. The Authority signs the root with Ed25519 and submits it to OpenTimestamps for Bitcoin anchoring.
Select any file to create a cryptographic seal. The file is streamed through BLAKE3 in your browser, building a Merkle tree from 64KB chunks. Only the cryptographic manifest is sent to the server.
The Authority signs the Merkle root with Ed25519 and submits the digest to OpenTimestamps calendar servers for Bitcoin anchoring. You receive a signed manifest, a PDF certificate, and a ledger entry with a shareable URL.
Re-upload the file to re-hash it and compare against the original seal. BitSeal verifies the Ed25519 signature, checks the ledger, and shows the Bitcoin anchor status. Full offline verification is also possible with the Python SDK.
Why it matters
Every seal is submitted to OpenTimestamps calendar servers and anchored to the Bitcoin blockchain. Once confirmed, the timestamp proves the file existed before a specific block, independent of BitSeal infrastructure.
The Ed25519 verification key is published at /.well-known/bitseal-authority.json and derived at runtime from the signing key. Any third party can verify a seal without trusting BitSeal servers.
Prove that a signed contract, proposal, or agreement has not been altered after the fact. A seal record provides cryptographic evidence of the original document state, anchored to Bitcoin for independent verification.
Regulatory submissions, audit artifacts, and chain-of-custody documents need provable integrity. BitSeal creates verifiable records without relying on a third-party notary service.
Seal release artifacts, configuration files, or build outputs so downstream consumers can verify that what they received matches what was published.
The open-source Python SDK verifies seals fully offline. Recompute the BLAKE3 Merkle root from the file, compare it to the manifest, and verify the Ed25519 signature against the published Authority key.
Built with
BitSeal uses BLAKE3 for file hashing and Merkle leaves, SHA3-512 as a second whole-file digest, Ed25519 for Authority signatures, and OpenTimestamps with Bitcoin as the decentralized anchor. Seals persist in Neon Postgres. The open-source Python SDK lets developers integrate sealing and verification into their own systems.
FAQ
Built by Orygn
Orygn builds custom software, internal tools, and security-focused systems for small businesses and growing teams. BitSeal is a working example of that approach applied to file integrity and provenance verification.
Open BitSeal